Azure Active Directory (AD), Explained
Azure Active Directory (AD) has been handling our identity requests since 2013, and is one of the most widely used cloud-based identity and access management services, with millions of users and thousands of organizations using it to manage access to their cloud-based applications and services. Azure AD has processed billions of authentications and millions of transactions daily, demonstrating its scalability and reliability.
And yet, there is a lot of confusion with Azure AD.
With everything moving to the cloud, Microsoft needed a way to authorize and authenticate users to cloud resources, including their own offerings like Microsoft 365 (Office 365). Microsoft made Azure AD, which is both an authorization and authentication provider.
Overview
Azure AD, although it shares branding with the decades old Active Directory (AD) that started shipping with Windows 2000 Server and that also handles identity requests, it bares little resemblance to AD and was made for cloud resources (Azure AD Application Proxy a feature of Azure AD can enable cloud to on-premise web access without the use of any remote tunnel).
Below is a comparison of Azure AD and AD.
| Azure AD | Active Directory | |
|---|---|---|
| Deployment Model | Cloud | On-premise |
| User management | User & groups, Admin. Units | User & groups, OUs |
| Authentication & Authorization | OAuth 2.0 & OpenID Connect | Kerberos & NTLM |
| Integration with Cloud Services | Seemless integrations | AD Federation Services (ADFS) |
| Scalability | Highly scalable | Limits from hardware/network resources |
| Cost | Subscription-based | Hardware, software, and maintenance |
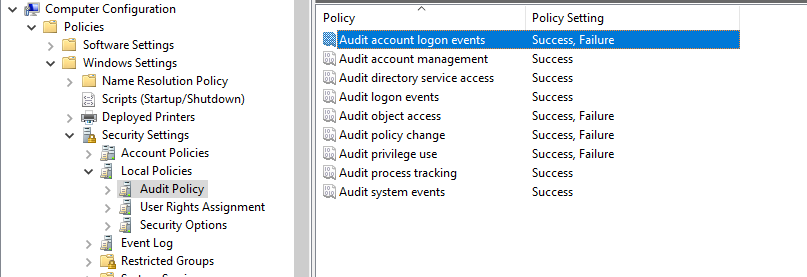
| Policy | Admin. templates1 | Group Policy, auth. polices and silos |
Continue reading for more.
Technical Details
Azure AD uses OAuth 2.0 and OpenID Connect (OIDC) for authorization and authentication respectfully.
OAuth 2.0 is a protocol that allows users to grant limited access to their resources on one site (called the “resource server”) to another site (called the “client”) without revealing their credentials. Azure AD acts as the authorization server in this scenario, allowing clients to obtain an access token that can be used to access specific resources on behalf of the user.
OpenID Connect is an authentication protocol built on top of OAuth 2.0, which provides identity information about the authenticated user in the form of a JSON Web Token (JWT). Azure AD acts as the identity provider in this scenario, providing authentication and user information to clients.
When a user attempts to access a resource protected by Azure AD, the client requests authentication and authorization from Azure AD. Azure AD responds with an OIDC authentication response that contains a JWT token containing information about the user. The client can then use the access token obtained through OAuth to access specific resources on behalf of the user.
Overall, Azure AD uses OAuth 2.0 and OpenID Connect to provide a secure and scalable identity management solution for cloud-based resources.
Tokens
JSON Web Token is a compact and secure way of transmitting information between two parties.
A JWT is a string consisting of three parts separated by dots - a header, a payload, and a signature. The header contains information about the type of token and the cryptographic algorithms used to secure it. The payload contains the data being transmitted, such as user information or authorization details. The signature is used to verify the integrity of the token and ensure that it has not been tampered with.
JWTs are often used for authentication and authorization in web applications and APIs. When a user logs in, a JWT is created containing the user’s identity information. This token is then included in subsequent requests to the server, allowing the server to verify the user’s identity and grant access to protected resources.
JWTs are also commonly used to share information between different services or systems, as they are easy to encode and decode and can be securely transmitted over the internet.
Applications
Enterprise applications (resource servers) need to be registered with your Azure AD tenant.
Populating
Azure AD can sync existing identities from an on-premise AD using software like Azure AD Connect/Cloud Sync or provision cloud-only identities by creating them in Azure AD through the Azure portal, command line tools, API, or templates.
User creation via templates might be reserved to service accounts and other non-employee accounts, making them apart of the infrastructure. Making the employee accounts data.
-
Provided by Microsoft Intune service ↩︎